Distmgr Log Failed To Generate The Encryption Key
- Release version 1606 of System Center Configuration Manager Current Branch contains many changes that are intended to prevent issues and improve features. The 'Issues that are fixed' list is not inclusive of all changes but instead captures what our product development team believes is most relevant to our broad customer base.
- Jun 02, 2014 Founder of System Center Dudes. Based in Montreal, Canada, Senior Microsoft SCCM Consultant, 5 times Enterprise Mobility MVP. Working in the industry since 1999.
- Feb 10, 2016 No actual functionality seemed to be affected but having this message reoccur 40+ times periodically certainly makes distmgr.log hard to follow and it doesn’t look good to the customer either. Cranking up the debug logging and log level for distmgr.log didn’t add any detail either.
- Delete existing encryption keys and unusable encrypted content when you cannot restore the symmetric key. Recreating Encryption Keys. If you have evidence that the symmetric key is known to unauthorized users, or if your report server has been under attack and you want to reset the symmetric key as a precaution, you can recreate the symmetric key.
May 23, 2018 Failed to configure IIS module, GLE - 1168 ConfigureIISModules failed to configure IIS module SQL MESSAGE: spProcessCcmCertBindingState - Updating CMRoleSSLCertificates for MYPULLDP.MYDOMAIN.NET state=1 Creating, reading or updating IIS registry key for a distribution point. IISPortsList in the SCF is '80'. IISSSLPortsList in the SCF is '443'. Sep 11, 2011 When you run the Windows Server 2003 SCW on a BITS-enabled distribution point, you must select Remote administration for IIS and related components on the Installed Options page of the SCW. If you do not enable remote administration for IIS and related components, the Windows Server 2003 SCW prevents the Configuration Manager 2007 Distribution. Labels: configmgr, Configuration Manager, DistMgr.log, failed, IsDPSiteSystemCertInstalled, mofcomp, sccm, smsdpprov.mof SCCM Recover Site - Lines displayed in 'Show Install Status' Just for information below lines taken from SCCM 'Show Install Status' after I do a recover (AdministrationOverviewSite ConfigurationSites / right click / 'Show.
Deleting and recreating encryption keys are activities that fall outside of routine encryption key maintenance. You perform these tasks in response to a specific threat to your report server, or as a last resort when you can no longer access a report server database.
Recreate the symmetric key when you believe the existing symmetric key is compromised. You can also recreate the key on a regular basis as a security best practice.
Delete existing encryption keys and unusable encrypted content when you cannot restore the symmetric key.
Recreating Encryption Keys
If you have evidence that the symmetric key is known to unauthorized users, or if your report server has been under attack and you want to reset the symmetric key as a precaution, you can recreate the symmetric key. When you recreate the symmetric key, all encrypted values will be re-encrypted using the new value. If you are running multiple report servers in a scale-out deployment, all copies of the symmetric key will be updated to the new value. The report server uses the public keys available to it to update the symmetric key for each server in the deployment.
You can only recreate the symmetric key when the report server is in a working state. Recreating the encryption keys and re-encrypting content disrupts server operations. You must take the server offline while re-encryption is underway. There should be no requests made to the report server during re-encryption.
You can use the Reporting Services Configuration tool or the rskeymgmt utility to reset the symmetric key and encrypted data. For more information about how the symmetric key is created, see Initialize a Report Server (SSRS Configuration Manager).
How to recreate encryption keys (Reporting Services Configuration Tool)
Disable the Report Server Web service and HTTP access by modifying the IsWebServiceEnabled property in the rsreportserver.config file. This step temporarily stops authentication requests from being sent to the report server without completely shutting down the server. You must have minimal service so that you can recreate the keys.
If you are recreating encryption keys for a report server scale-out deployment, disable this property on all instances in the deployment.
Open Windows Explorer and navigate to drive:Program FilesMicrosoft SQL Serverreport_server_instanceReporting Services. Replace drive with your drive letter and report_server_instance with the folder name that corresponds to the report server instance for which you want to disable the Web service and HTTP access. For example, C:Program FilesMicrosoft SQL ServerMSRS10_50.MSSQLSERVERReporting Services.
Open the rsreportserver.config file.
For the IsWebServiceEnabled property, specify False, and then save your changes.
Start the Reporting Services Configuration tool, and then connect to the report server instance you want to configure.
Generate a ssh key github. On the Encryption Keys page, click Change. Click OK.
Restart the Report Server Windows service. If you are recreating encryption keys for a scale-out deployment, restart the service on all instances.
Re-enable the Web service and HTTP access by modifying the IsWebServiceEnabled property in the rsreportserver.config file. Do this for all instances if you are working with a scale out deployment.
How to recreate encryption keys (rskeymgmt)
Disable the Report Server Web service and HTTP access. Use the instructions in the previous procedure to stop Web service operations.
Run rskeymgmt.exe locally on the computer that hosts the report server. Use the -s argument to reset the symmetric key. No other arguments are required:
Restart the Reporting Services Windows service.
Deleting Unusable Encrypted Content
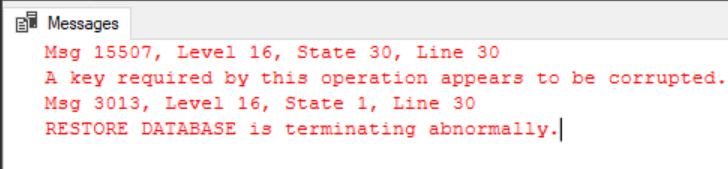
Distmgr Log Failed To Generate The Encryption Key Password
If for some reason you cannot restore the encryption key, the report server will never be able to decrypt and use any data that is encrypted with that key. To return the report server to a working state, you must delete the encrypted values that are currently stored in the report server database and then manually re-specify the values you need.
Deleting the encryption keys removes all symmetric key information from the report server database and deletes any encrypted content. All unencrypted data is left intact; only encrypted content is removed. When you delete the encryption keys, the report server re-initializes itself automatically by adding a new symmetric key. The following occurs when you delete encrypted content:
Connection strings in shared data sources are deleted. Users who run reports get the error 'The ConnectionString property has not been initialized.'
Stored credentials are deleted. Reports and shared data sources are reconfigured to use prompted credentials.
Reports that are based on models (and require shared data sources configured with stored or no credentials) will not run.
Subscriptions are deactivated.
Once you delete encrypted content, you cannot recover it. You must re-specify connection strings and stored credentials, and you must activate subscriptions.
You can use the Reporting Services Configuration tool or the rskeymgmt utility to remove the values.
Distmgr Log Failed To Generate The Encryption Key In Computer
How to delete encryption keys (Reporting Services Configuration Tool)
Start the Reporting Services Configuration tool, and then connect to the report server instance you want to configure.
Click Encryption Keys, and then click Delete. Click OK.
Restart the Report Server Windows service. For a scale-out deployment, do this on all report server instances.
How to delete encryption keys (rskeymmgt)
Distmgr.log Failed To Generate The Encryption Key
Run rskeymgmt.exe locally on the computer that hosts the report server. You must use the -d apply argument. The following example illustrates the argument you must specify:
Restart the Report Server Windows service. For a scale-out deployment, do this on all report server instances.
How to re-specify encrypted values
For each shared data source, you must retype the connection string.
For each report and shared data source that uses stored credentials, you must retype the user name and password, and then save. For more information, see Specify Credential and Connection Information for Report Data Sources.
For each data-driven subscription, open each subscription and retype the credentials to the subscription database.
For subscriptions that use encrypted data (this includes the File Share delivery extension and any third-party delivery extension that uses encryption), open each subscription and retype credentials. Subscriptions that use Report Server e-mail delivery do not use encrypted data and are unaffected by the key change.
See Also
Distmgr Log Failed To Generate The Encryption Key In Excel
Configure and Manage Encryption Keys (SSRS Configuration Manager)
Store Encrypted Report Server Data (SSRS Configuration Manager)